In a video released yesterday by the Russian propaganda news channel RT, Russian special forces were shown training members of Liwa al Quds, a pro-regime Palestinian militia group in Syria.
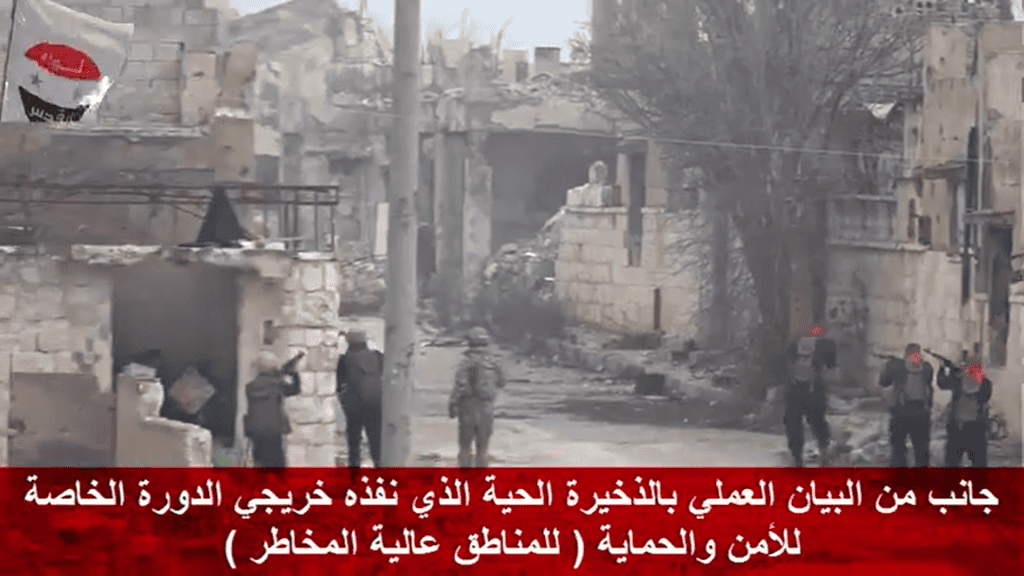
The video’s description said that the militants are being taught “storming fortified positions.”
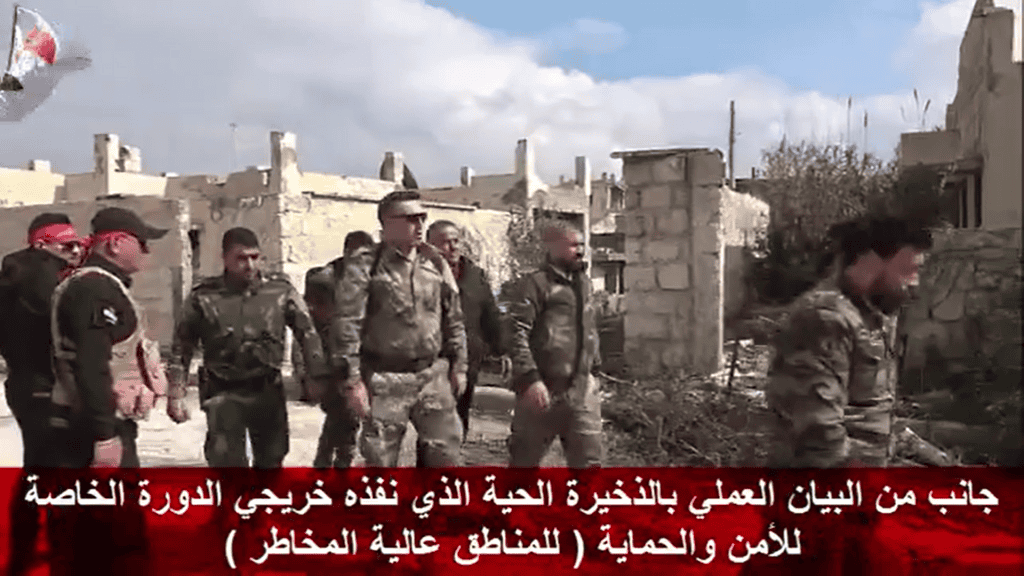
On Liwa al Quds’ Facebook page, the group said these are graduates of a Russian-ran “high threat area” training course. The video published on its Facebook page offers a different angle of the RT video, in which Syrian and Russian military officers can be seen overlooking the training.
Liwa al Quds is one of Russia’s favorite militia groups inside Syria. Russian officers have bestowed several medals to the group’s commanders, while Russian troops have embedded with the group on several occasions.
Pictures released by the group have also shown more modern Russian weapons within its arsenal, indicating that Russia has directly armed the group. Some members of the militia can be seen wearing Russian military gear in today’s video, as well.
For its part, Liwa al Quds proudly displays its ties to Russia on its Facebook page by often sharing photos of Russian troops among its soldiers. It also routinely shares news regarding to Vladimir Putin or Russia’s international activities, especially in Syria.
Liwa al Quds, which also refers to itself as the Syrian Arab Army Fedayeen, is a largely Sunni Palestinian militant group that has openly operated as an auxiliary to pro-regime forces in Syria since 2013. It has taken part in regime offensives such as in Aleppo, Deir al Zour, and in the Homs desert, where it has also fought alongside several Iranian-controlled groups.
Screenshots from Liwa al Quds’ video of the training exercises:


Are you a dedicated reader of FDD's Long War Journal? Has our research benefitted you or your team over the years? Support our independent reporting and analysis today by considering a one-time or monthly donation. Thanks for reading! You can make a tax-deductible donation here.







1 Comment
This isn’t going to end well for someone.