|
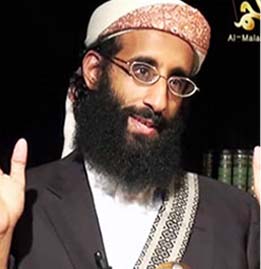
Said Ali al Shihri, former Guantanamo detainee and deputy leader of al Qaeda in Yemen. Photo from The SITE Institute. |
The Yemen Post is reporting that Said al Shihri, al Qaeda in the Arabian Peninsula’s deputy leader and a former Guantanamo Bay detainee, was killed when a bomb he was assembling detonated prematurely. The following report has not been confirmed:
Private sources told the Yemen Post that the second in command of Yemen- based Al-Qaeda in the Arabian Peninsula (AQAP) was killed in a bomb explosion while he was preparing it to be used against Yemeni and foreign targets.
Keep in mind that on several occasions in the past, Yemeni security officials have claimed that Shihri, and other top AQAP leaders, have been captured or killed. AQAP hasn’t released a statement announcing his death, either.
Are you a dedicated reader of FDD's Long War Journal? Has our research benefitted you or your team over the years? Support our independent reporting and analysis today by considering a one-time or monthly donation. Thanks for reading! You can make a tax-deductible donation here.








8 Comments
Yeah, barring DNA proof from Quantico or hard confirmation from AQAP, I’m gonna figure this is the Saleh government trying to throw off scrutiny and US pressure in the wake of the Egyptian Revolution.
However, interesting that the reported cause of death is ‘accidental detonation’ during a bomb-making session. Shades of the ‘official government story’ from Pakistan on the death of Abu Hamza Rabia in Pakistan 2005. Really one of the earliest CIA drone strikes in that country.
IIRC, that was also the explanation the Saleh government used regarding the 2002 Predator strike in Yemen that killed al-Harithi…the car bomb he was riding in went off early.
If you are not aware the target has been hit with a Hellfire and you know he makes bombs then you are likely to jump to the conclusion that he blew himself up. You don’t need misdirection to get there. It could be used later, of course.
I think the two examples you cite are cases where the local government didn’t know that they’d been hit by a Hellfire.
The details of the 2002 Yemeni strike against Abu Ali al-Harithi was written up by James Bamford with input from NSA folks. The NSA intercepted a call on a sat phone number from the vehicle in motion that they knew was associated with the target. A linguist couldn’t ID the voice until they overheard the main target talking in the back seat. He recognized that voice. They then tasked a drone onto the vehicle and hit it. The didn’t know there was an American in there until later. It was a very closed loop. The Yemeni government didn’t know until some time later too (I suspect).
Summarized here
http://www.msnbc.msn.com/id/10549887/ns/nightly_news/
How sad ;_)
IMHO, at least this is encouraging. I know for a fact that the technology exists, it just needs the creative minds to deploy it.
As Bill has said, the technology can only be as good as the minds and strategies that are behind it.
What I am referring to here is if they can somehow “bug” the vehicles (with GPS tracking chips in the computer hardware or elsewhere) BEFORE the terrorists acquire them.
The same can apply to their computer hardware (with an emphasis on the motherboards or possibly even the keyboards).
For example, my computer is encrypted. However, when I power it on, I key in a pass code and whether I like it or not, my system is vulnerable to remote hardware interception (since I have no firewall or antivirus software active at least at that point).
If they could develop some kind of hardware manipulation to remotely read and transmit a terrorists keystrokes in real time it may yield an intelligence bonanza. (Just an idea, surreptitiously embed cell phone circuitry in the motherboard or keyboard).
And, if they can get to the point where they can “conveniently/prematurely” and remotely detonate their bombs (at a most inopportune time at least from their perspective) what you’d have would be “the perfect storm,” or accident or so they would believe.
Any strategy has to begin with an idea.
I’d like to add with emphasis to the above, that once we’ve got their computers and vehicles adequately bugged, that’s it, game over for them.
Their is a whole new front to this war we have yet to exploit. That front is cyberspace (or the internet).
It would indeed be like “POETIC JUSTICE,” if we could surreptitiously get 9-1-1 circuitry (and software) onto their systems.
IMHO, religion aside and at their base, they ain’t nothing but a bunch of hardcore and incorrigible criminals right from the get go.
Talk about being literally hoist with his own petard! Sweet!
Charu, I’m quite impressed by your linguistic skill.
I’ll admit, I had to look up the phrase “hoist with his own petard,” (thank God for google).
Could it be that you’ve mastered a better command of the English language than most of US?
Anyways, I guess as it now turns out this guy isn’t dead after all. Oh well, let’s just hope for better luck next time.
@ James
Your idea of bugging keyboards was implemented
back in the 60s. I met an old CIA guy who told
me how it turned out that each key on an electric typewriter has a different EM signature, and that
you could figure out what has been typed inside
a building by sitting in a car in the parking lot and
detecting these small emissions.
Of course, today it is actually much easier, we
just need to plant a key-stroke logger virus on
their machines, and this is easily done by breaking into jihadi websites, and putting the virus into one of
the links. It is hard to imagine that this isn’t
already being done. And when I put this to
a former FBI guy who used to work on this stuff,
he told me “don’t worry, it is”.