Today I was a panelist at the rollout event for a new report published by the Brennan Center for Justice at the New York University School of Law, Emily Berman’s Domestic Intelligence: New Powers, New Risks. The report — which is focused on the expansion of investigatory powers in the 2008 Attorney General’s Guidelines for Domestic FBI Operations — advocates restricting situations in which the FBI can use highly intrusive investigative techniques; prohibiting “improper consideration of race, religion, ethnicity, national origin, or First-Amendment-protected activity”; and increasing oversight of the FBI’s use of its authority.
The report raises legitimate issues, and makes a
contribution — in particular, in its explanation of how investigatory standards have loosened since the Church Committee reforms in the 1970s. However, I emerged skeptical of its recommendation to limit the FBI’s investigative powers because I felt the report did not provide a full picture of what the impact would be on law enforcement efforts.
Context is key
In reviewing past FBI abuses — or, in Berman’s phraseology, “misplaced
domestic intelligence efforts” — the report twice singled out the same
Cold War-era effort, called the Library Awareness Program. As the report
recounts, this program “included regular FBI visits to public libraries
seeking information regarding individuals who read scientific and
technical journals, sometimes asking librarians to be wary of
‘foreigners’ or persons with ‘East European or Russian-sounding names.'”
This of course sounds absurd on its face: a blanket suspicion of
foreigners looking for scientific or technical information?
What the report does not mention is that during this period — in the
1980s — a man named Mahdi Obeidi was doing just that. Obeidi was
Saddam Hussein’s chief nuclear scientist, charged
with rejuvenating Iraq’s nuclear program after Israel destroyed the
Osiraq nuclear reactor in 1981. Saddam was fixated on
building a nuclear program that could not be easily subjected to attack
the way his above-ground reactor had been. He settled on centrifuge
technology, which creates great centrifugal force by rotating at
extremely high speeds, thus separating the heavier uranium-238 isotopes
from lighter uranium-235 isotopes. After uranium-238 has been drawn
out, the highly-enriched uranium remaining at the center can be siphoned
away. For a country trying to create a nuclear weapon, centrifuges are easier to hide and to protect than
above-ground reactors.
Obeidi, in his book The Bomb in My Garden,
describes how he was able to
create a working prototype of a magnetic centrifuge for Saddam Hussein
prior to Iraq’s 1990 invasion of Kuwait. A large part of the research
involved traveling through the US to glean the requisite knowledge
from scientists who rather naively put their trust in him; the
idea that Obeidi might be an
agent of a foreign power was simply outside their frame of reference. He
obtained a significant piece of information, which proved to be a key
part of the centrifuge program, from the University of Virginia’s
library. Obeidi had asked the librarian if he could see a critical
report on
centrifuge technology called the Zippe report. Asked to fill out a
lengthy form and provide identification for security reasons, Obeidi
instead asked: “Would it
be possible to ensure that the report is indeed here before I fill out
all these forms for it?”
The librarian brought him the report, and
insisted that Obeidi fill out
the forms before he read it. Obeidi, hesitant to do
so, asked: “Could I see it for a moment to be sure it is the right
document?” There, right in front of the librarian, he flipped through
the report — and found, in the back, an appendix listing all recipients
of the report when it was first issued in 1960. A look at
those names enabled Obeidi to get his hands on the report itself —
which in turn helped him build a centrifuge prototype.
So while
Berman’s report, without any further rationale or analysis, dismisses as
far-fetched the FBI’s concern about foreigners who were interested in
scientific or technical information, the Bureau’s concern was not
misplaced. In fact, key technical information that a
foreign agent gleaned from a US library proved central to the
astounding development of Iraq’s nuclear program in the 1980s. This
shows us that context is key — and a large part of my skepticism about
Berman’s report is its failure to contextualize the law enforcement
impact of the changes it proposes.
Does it make us safer?
I find it hard to believe
that following the report’s guidance would make us both freer and also
safer. Berman argues that the report’s recommendations actually improve policing efforts in two
ways: by reducing the deluge of information that confronts law
enforcement, and also by harmonizing relations between law enforcement and affected communities (in
particular the Muslim community) by reducing feelings of stigmatization.
As
to the first point, reducing the deluge of information, it
is true that analysts have trouble keeping up with the volume of threat
reporting. But that doesn’t mean that depriving them of information
therefore automatically improves analytic efforts. The question is: Would the report’s recommendations take away information that is truly
unnecessary, or would they
deprive law enforcement of information that it needs to more
effectively do its job? The report’s arguments on this point are, to put
it mildly, unconvincing. Given the lack of consultation with law
enforcement in producing the report, it is highly implausible that an
attorney with no investigatory background somehow stumbled upon the
magic formula to make the FBI more effective
by depriving it of investigatory authority. Among other things, this view assumes an almost
cartoonish incompetence on the part of agents in the field that is not
reflected in my experiences with the Bureau.
As to Berman’s second point, that this report’s recommendations would improve
relations between the FBI and the Muslim community, that may or may not
be true. But there are other ways to address the problem without
limiting the Bureau’s investigative authority; such as training dedicated to the
issue, and strong directives dealing with how to more effectively approach
investigations without alienating critical communities.
Terrorist profiling
The main claim that Berman makes for her recommendations as a net positive for
law enforcement effectiveness is that they would reduce instances of terrorist
profiling. How much they would so is not clear after a couple of careful
readings. The report’s exact recommendation is to “[p]rohibit improper
consideration of race, religion, ethnicity, national origin, or
First-Amendment-protected activity in investigative decisions.” This is a
rather imprecise line — but regardless of where exactly the report
draws the line, it’s clear that it has a more restrictive approach to
terrorist profiling than the 2008 guidelines provide.
Indeed, it
is evident that Berman’s report views profiling as an ineffective tool all
around; it speaks, for example, of an alleged “general consensus that
profiling is ineffective.” But the main factor that tends to hamper
discussions of profiling is lack of clarity about what the practice
means. Berman notes: “In the past, law enforcement organizations have
successfully policed groups engaged in organized violence — like the
mafia or the KKK — without trenching on the civil liberties of the
entire Italian-American or Southern Christian communities.” This is fair
enough, but when informed analysts speak of a terrorist profile, they
are not suggesting that the entire Muslim community should be viewed as
suspect.
A better question is: Can the factors singled out by Berman’s
report as particularly problematic — religion, race, ethnicity,
national origin, or protected First Amendment activities — be
relevant when law enforcement authorities are determining whether to deepen an
investigation? It seems clear to me that such factors can have legitimate relevance, as I will flesh out
with three examples:
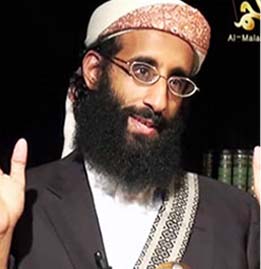
- A Muslim psychiatrist in the US
military is found to be in communication with a high-profile terrorist
recruiter in Yemen. This psychiatrist has also given several
presentations outlining his views on Islam to his command. Is profiling
these views — to see whether they map with what some dub the “salafi
jihadi” interpretation of the faith, thus indicating a possible danger
— appropriate?
- A college dropout in Arizona is posting on
extreme right-wing web sites. He has a great amount of anti-government
anger, which is focused in particular on his local congresswoman. These
political views are protected by the First Amendment. Moreover, his
views at first blush seem to map with those of the racist and
apocalyptic Christian Identity movement. Is probing these views —
because they constitute “First-Amendment-protected activity” and
religion — unacceptable in determining whether he poses a threat?
[Note: Though loosely based on the Jared Lee Loughner case, this fact
pattern departs somewhat from it.]
- There is a jihadist web
site, which Berman’s report counsels against “profiling” on two levels.
First, the site itself contains religious content. And second, the
speech on the web site, though extremely anti-US, is itself protected
by the First Amendment. Should investigators be allowed to chat with
individuals on the site to determine whether they intend to carry out
attacks?
Further investigation of the jihadist web site would seem to be disallowed by
Berman’s recommendations, in that the report says the FBI should be
prohibited from “posing as other people … and recruiting informants to
glean more information in the absence of some factual basis for
suspicion.” Though these methods have been controversial, there were two arrests
in 2009 — of Michael Finton and Hosam Smadi — that used these
techniques. In both cases, the defendants literally pushed the button
that they thought would set off a bomb during the course of sting
operations.
Threat environment
Right now we’re in the midst of an era that is likely to see more
extremism and more violence designed to disrupt the system on which our
lives depend. Against such a backdrop we must be sure to safeguard civil
liberties — because it is all too easy to discard our cherished
liberties in the name of security — but we must also be attentive to
what powers law enforcement needs to keep us safe.
Extremism
itself can be as potent a threat to liberty as abuses inflicted by
government. Ask Molly Norris, the Seattle cartoonist who conceived of
“Everybody Draw Mohammed Day” after Comedy Central refused to air a
picture of Muhammad on their hit show South Park (even though
that same episode depicted Buddha snorting cocaine and Jesus looking at
Internet pornography). After threats to her life, she has disappeared
— as though she never existed. Ask Theo van Gogh, who was brutally
murdered on the streets of Amsterdam after producing a film critical of
the treatment of women in Islam. And ask Rep. Giffords.
So Berman’s report asks some important questions. It makes a
contribution. But I think its recommendations, if followed, would almost
certainly make us less safe. Because the report doesn’t acknowledge
that fact, I find it difficult to evaluate whether the proposals it
advances for stripping the FBI of its investigative authority would in
fact be worth the cost.
Are you a dedicated reader of FDD's Long War Journal? Has our research benefitted you or your team over the years? Support our independent reporting and analysis today by considering a one-time or monthly donation. Thanks for reading! You can make a tax-deductible donation here.







5 Comments
So I would ask, Did the people on the panel agree or disagree with your position?
I was shocked to read about Molly Norris’ forced disappearance. To the best of my knowledge, this sad episode has been completely under the radar and has elicited no widespread outrage in the media. This is so wrong! Her work should appear in every publication in the US. We are all Molly Norris and we should collectively not be cowed by these fundamentalist threats of violence. E pluribus unum!
If Ayaan Hirsi Ali can be provided security and go about her business (albeit carefully) in this country, unlike the cowardly Dutch who washed their hands off her, then Molly Norris should also have every opportunity not to have to “disappear” out of fear of her safety. The Feds ought to grab this opportunity to smoke out the jihadists in our midst, and not to kowtow to them. This is shameful!!!
A question the writer would be… What do you mean by “the racist and apocalyptic Christian Identity movement” I am unfamiliar with this term, could you explain how you picked this term when describing a young man with mental illness? and just what does it mean?
Mark: The panel was stacked against my position, so they disagreed. I don’t use “stacked” pejoratively, since it was the Brennan Center’s roll-out of its own report. It would be odd if they introduced the report to the world via a panel filled with skeptics.
Danny: You always have to treat Wikipedia skeptically, but its entry on Christian Identity does a decent job of explaining that belief system: http://en.wikipedia.org/wiki/Christian_identity. Let me be very clear: I have no reason to believe that Loughner was actually part of the Christian Identity movement, and given the lack of information on any such connection, we should assume that it doesn’t exist. This is why I noted that “[t]hough loosely based on the Jared Lee Loughner case, this fact pattern departs somewhat from it.” I included the Christian Identity connection for two reasons. First, it arguably would have provided a greater indication at the outset that he could pose a danger. And second, by the report’s criteria, authorities should have been especially hesitant to explore those views because they were religious in nature. In that way, I was challenging the report’s basic paradigmatic assumption that using these factors as part of a threat profile is repugnant, and ineffective.
Sorry to hear the panel was stacked but I’m not surprised. Thanks for keeping us up to date.